
AIMCOM2 Program
The 28th IEEE International Conference on Network Protocols (ICNP 2020)
Madrid, Spain,
October 13,
2020 Follow @IEEE_ICNP
Online participation in ICNP 2020 is exclusively via the ICNP-specific Whova site available in app and web versions.
All times are in CEST. See program at a glance.
Technical Program
10:30 am - 10:35 am Welcome (Slides, Video)
10:35 am - 12:05 pm Session A (Video)
Session chair: Rongpeng Li (Zhejiang University, China)
A Blind CSI Prediction Method Based on Deep Learning for V2I Millimeter-Wave Channel (30min,
Paper,
Slides,
Video)
Jingxiang Yang, Liyan Li, and Min-Jian Zhao (Zhejiang University, China)
Context-Aware Clustering for SDN Enabled Network (30min,
Paper,
Slides,
Video)
Ran Duo, Celimuge Wu, Yoshinaga Tsutomu (University of Electro-Communications, Japan), and Yusheng
Ji (National Institute of Informatics, Japan)
Real-World ADS-B signal recognition based on Radio Frequency Fingerprinting (30min,
Paper,
Slides,
Video)
Haoran Zha, Qiao Tian, and Yun Lin (Harbin Engineering University, China)
12:05 pm - 12:30 pm Tea/Coffee Break
12:30 pm - 02:00 pm Session B (Video)
Session chair: Rongpeng Li (Zhejiang University, China)
[Invited] Towards Smart and Reconfigurable Environment: Intelligent Reflecting Surface
Enabled 6G Wireless Networks
(30min, Bio, Abstract,
Slides,
Video)
Qingqing Wu (University of Macau, China)
[Invited] Bring AI into 5G Radio Access Network
(30min, Bio, Abstract,
Video)
Qi Sun (China Mobile Research Institute, China)
[Invited] AI-Based Physical Layer and Protocol Design towards beyond 5G/6G Radio Access
Networks
(30min, Bio, Abstract,
Slides,
Video)
Maziar Nekovee (University of Sussex, UK)
02:00 pm - 03:30 pm Lunch Break
03:30 pm - 05:00 pm Session C (Video)
Session chair: Rongpeng Li (Zhejiang University, China)
Machine Learning at the Edge: Efficient Utilization of Limited CPU/GPU Resources by
Multiplexing
(30 min, Paper,
Slides,
Video)
Aditya Dhakal (University of California, Riverside, USA), Sameer G Kulkarni (Indian Institute of
Technology, Gandhinagar, India), and K. K. Ramakrishnan (University of California, Riverside, USA)
[Keynote] Edge Intelligence in IoT Ecosystems: A Continual Edge Learning
Approach
(45 min + 15 min discussion, Bio, Abstract,
Video)
Junshan Zhang (Arizona State University, USA)
05:00 pm - 05:30 pm Tea/Coffee Break
05:30 pm - 07:00 pm Session D (Slides, Video)
Session chair: Hulya Seferoglu (University of Illinois at Chicago, USA)
[Keynote] Adversarial Machine Learning
(45 min + 15 min discussion, Bio, Abstract,
Video)
Ananthram Swami (ARL, USA)
[Invited] Vulnerabilities of Voice Assistants at the Edge: From Defeating Hidden Voice
Attacks to Audio-based Adversarial Attacks
(30 min, Bio, Abstract,
Slides,
Video)
Yingying (Jennifer) Chen (Rutgers University, USA)
07:00 pm Closing (Slides, Video)
Keynote and Invited Talk Speakers

Junshan Zhang (Arizona State University, USA)
Prof. Zhang is a Fellow of the IEEE, and a recipient of the ONR Young Investigator Award in 2005 and the NSF
CAREER award in 2003. He received the IEEE Wireless Communication Technical Committee Recognition Award in
2016. His papers have won a few awards, including the Kenneth C. Sevcik Outstanding Student Paper Award of
ACM SIGMETRICS/IFIP Performance 2016, the Best Paper Runner-up Award of IEEE INFOCOM 2009 and IEEE INFOCOM
2014, and the Best Paper Award at IEEE ICC 2008 and ICC 2017. Building on his research findings, he
co-founded Smartiply Inc in 2015, a Fog Computing startup company delivering boosted network connectivity
and embedded artificial intelligence for IoT applications.
Prof. Zhang was TPC co-chair for a number of major conferences in communication networks, including IEEE
INFOCOM 2012 and ACM MOBIHOC 2015. He was the general chair for ACM/IEEE SEC 2017, WiOPT 2016, and IEEE
Communication Theory Workshop 2007. He was a Distinguished Lecturer of the IEEE Communications Society. He
was an Associate Editor for IEEE Transactions on Wireless Communications, an editor for the Computer Network
journal, and an editor IEEE Wireless Communication Magazine. He is currently serving as an editor-at-large
for IEEE/ACM Transactions on Networking and an editor for IEEE Network Magazine.
Keynote 1: Edge Intelligence in IoT Ecosystems: A Continual Edge Learning Approach
Abstract: Many IoT applications demand intelligent decisions in a real-time manner. The necessity of real-time edge intelligence dictates that decision making takes place right here right now at the network edge. Since an edge node often has a limited amount of data and is constrained with computational resources, we advocate continual edge learning to achieve edge intelligence. To this end, we develop an edge learning framework where the edge node learns its model based on local data in real-time, while leveraging the cloud knowledge transfer or learning from peer edge nodes.
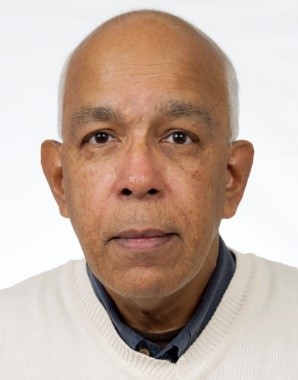
Ananthram Swami (ARL, USA)
Ananthram Swami is with the US Army CCDC Army Research Laboratory and is the Army's Senior Research Scientist (ST) for Network Science. Prior to joining ARL, he held positions with Unocal Corporation, the University of Southern California, CS-3 and Malgudi Systems. He was a Statistical Consultant to the California Lottery, developed a MATLAB-based toolbox for non-Gaussian signal processing. He has held visiting faculty positions at INP, Toulouse and Imperial College, London. He received the B.Tech. degree from IIT-Bombay; the M.S. degree from Rice University, and the Ph.D. degree from the University of Southern California (USC), all in Electrical Engineering. Swami's work is in the broad area of network science. He is an ARL Fellow and a Fellow of the IEEE.
Keynote 2: Adversarial Machine Learning
Abstract: Modern machine learning systems are susceptible to adversarial examples; inputs that preserve the characteristic semantics of a given class, but whose classification is incorrect. Current approaches to defense against adversarial attacks rely on modifications to the input (e.g. quantization, randomization) or to the learned model parameters (e.g. via adversarial training), but are not always successful. This talk will include: 1) Overview of attacks on machine learning and defenses. 2) Discussion of the enablers of successful adversarial attacks via theory, and empirical analysis of commonly used datasets. 3) Discussion of recently proposed defenses that change the representation of the model outputs, drawing upon insights from coding theory. 4) Novel approaches to detection of adversarial examples using confidence metrics. The talk will conclude with a discussion of issues in distributed ML in coalition operations.

Qingqing Wu (University of Macau, China)
Qingqing Wu (S'13-M'16) received the B.Eng. and the Ph.D. degrees in Electronic Engineering from South
China University of Technology and Shanghai Jiao Tong University (SJTU) in 2012 and 2016, respectively. He
is currently an assistant professor in the Department of Electrical and Computer Engineering at the
University of Macau, China, and also affiliated with the State key laboratory of Internet of Things for
Smart City. He was a Research Fellow in the Department of Electrical and Computer Engineering at National
University of Singapore. His current research interest includes intelligent reflecting surface (IRS),
unmanned aerial vehicle (UAV) communications, and MIMO transceiver design. He has published over 70 IEEE
journal and conference papers.
He was the recipient of the IEEE WCSP Best Paper Award in 2015, the Outstanding Ph.D. Thesis Funding in SJTU
in 2016, the Outstanding Ph.D. Thesis Award of China Institute of Communications in 2017. He was the
Exemplary Editor of IEEE Communications Letters in 2019 and the Exemplary Reviewer of several IEEE journals.
He serves as an Associate Editor for IEEE Communications Letters, IEEE Open Journal of Communications
Society, and IEEE Open Journal of Vehicular Technology. He is the Lead Guest Editor for IEEE Journal on
Selected Areas in Communications on "UAV Communications in 5G and Beyond Networks", and the Guest
Editor for IEEE Open Journal on Vehicular Technology on "6G Intelligent Communications" and IEEE
Open Journal of Communications Society on "Reconfigurable Intelligent Surface-Based Communications for
6G Wireless Networks". He is the workshop co-chair for IEEE ICC 2019-2021 workshop on "Integrating
UAVs into 5G and Beyond", and the workshop co-chair for IEEE GLOBECOM 2020 workshop on "Reconfigurable
Intelligent Surfaces for Wireless Communication for Beyond 5G". He serves as the Workshops and Symposia
Officer of Reconfigurable Intelligent Surfaces Emerging Technology Initiative and Research Blog Officer of
Aerial Communications Emerging Technology Initiative.
Invited Talk I: Towards Smart and Reconfigurable Environment: Intelligent Reflecting Surface Enabled 6G Wireless Networks
Abstract: In this talk, we introduce a new wireless research paradigm by employing a massive number of low-cost passive reflecting elements with controllable phase, named intelligent reflecting surface (IRS), which is able to smartly change the wireless signal propagation to enable various functions such as beamforming and interference nulling/cancelation. We illustrate the main applications of IRS in achieving spectrum and energy efficient as well as secure and sustainable wireless networks in the future, and its advantages as compared to existing technologies such as massive MIMO and active relaying. We then present the signal and channel model of IRS by taking into account its hardware limitation in practice. Next, we focus on discussing the main design challenges in IRS-aided wireless networks, including joint active and passive beamforming optimization, channel estimation, etc., and highlight important directions for future work.

Qi Sun (China Mobile, China)
Dr. Qi Sun is a Senior Researcher in China Mobile Research Institute, Co-chair of O-RAN WG2, Chairman of ITU-T Focus Group on Machine Learning for Future Networks including 5G (FG-ML5G) Data formats & ML technologies Group. She has been working on the key technology and standardization of 5G radio access network. Now her research interest focuses on wireless big data and AI for 5G and future RAN architecture, protocol and algorithm design. She has filed more than 50 patents, published more than 30 SCI/EI papers, and won the award of ESI top 1% highly cited paper.
Invited Talk II: Bring AI into 5G Radio Access Network
Abstract: With the global deployment and commercialization of the 5G network, Wireless big data and ML/AI are widely recognized as the essential element to drive 5G network intelligence evolution in order to deliver the necessary efficiency, flexibility, and cost effectiveness. Significant progress and validation on the network operation and maintenance using ML/AI technologies have been made in 4G/5G networks. Various study on the network intelligence standardization from management to control planes, including use cases and requirements, AI functional framework, procedures and architecture have been actively explored. This talk will explore the journey of pursuing native RAN intelligence, from theory to preliminary practice validation. The AI/ML use cases in 5G network and some validations results will be shared followed by the standardization progress. Further, the challenges and gaps are shared based on the lessons learned from the practice so far.

Maziar Nekovee (University of Sussex, UK)
Maziar Nekovee is currently a Professor of telecom and mobile technologies and Dean of Sussex Zhejiang GongShang joint AI Institute at University of Sussex, UK. He is also Vice Chair of NetWorld 2020 European Technology Platform where he is chair of Working Group on Future Technologies. His current research focuses on AI for radio access and core network design, THz communication for beyond-5G/6G mobile communication, future Internet architecture and IP design for future verticals. Prior to joining U. Sussex in 2017, he was Head of Samsung's European research and collaboration in 5G, where he developed new radio access technologies operating in millimetre-wave bands, which were subsequently implemented in the 5G New Radio (5G NR) industry standard by 3GPP. Prior to Samsung he was with BT Research and Innovation where he worked on a range of fixed and wireless technologies, including cognitive radio/dynamic spectrum sharing, WiFi-based V2X, and gossip/epidemic protocols for reliable multicast communication. Maziar is the author of 100+ papers, 15 patents and one book. He has a PhD in Physics and a first degree in EEE, both from the Netherlands.
Invited Talk III: AI-Based Phsyical Layer and Protocol Design towards beyond 5G/6G Radio Access Networks
Abstract: 5G technologies are expected to enable new verticals, services, and business models. Recently, the use of artificial intelligence (AI) and data analytics is shown to provide massive advantages in terms of reducing network complexity and enhancing its performance. In this talk , I provide an overview of the recent studies on AI-assisted solutions in 5G and beyond-5G wireless networks, followed by three case studies of our recent research, including a Q-learning-assisted cell selection mechanism, an AI engine that enables intelligent 5G fronthaul slicing, multiple radio access technology (RAT) spectrum sharing in millimeter-wave bands via reinforcement learning-based beam management and the application of deep neural network auto-encoders for beyond-5G physical layer design. The recent industry and standardization activities of using AI in 5G networks are summarized.

Yingying (Jennifer) Chen (Rutgers University, USA)
Yingying (Jennifer) Chen is a Professor of Electrical and Computer Engineering and Peter Cherasia Faculty Scholar Endowed Professor at Rutgers University. She is the Associate Director of Wireless Information Network Laboratory (WINLAB). She also leads the Data Analysis and Information Security (DAISY) Lab. She is an IEEE Fellow. Her research interests include mobile sensing and computing, cyber security and privacy, Internet of Things, and smart healthcare. Her background is a combination of Computer Science, Computer Engineering and Physics. She was a tenured professor at Stevens Institute of Technology and had extensive industry experiences at Nokia previously. She has published over 200 journal articles and conference papers and 8 patents. She is the recipient of multiple Best Paper Awards from EAI HealthyIoT 2019, IEEE CNS 2018, IEEE SECON 2017, ACM AsiaCCS 2016, IEEE CNS 2014 and ACM MobiCom 2011. She is also the recipient of NSF CAREER Award and Google Faculty Research Award. She received NJ Inventors Hall of Fame Innovator Award and is also the recipient of IEEE Region 1 Technological Innovation in Academic Award. Her research has been reported in numerous media outlets including MIT Technology Review, CNN, Fox News Channel, Wall Street Journal, National Public Radio and IEEE Spectrum. She has been serving/served on the editorial boards of IEEE Transactions on Mobile Computing (IEEE TMC), IEEE Transactions on Wireless Communications (IEEE TWireless), IEEE/ACM Transactions on Networking (IEEE/ACM ToN) and ACM Transactions on Privacy and Security.
Invited Talk IV: Vulnerabilities of Voice Assistants at the Edge: From Defeating Hidden Voice Attacks to Audio-based Adversarial Attacks
Abstract: Voice access technologies are widely adopted in mobile and voice assistant systems at the edge to serve as both critical and convenient ways for user interaction. Recent studies have demonstrated various vulnerabilities of voice assistant systems. One serious attack is to use synthetically rendered adversarial sounds embedded within a voice command to trick the speech recognition process into executing malicious commands, without being noticed by legitimate users. We show that by employing low-cost motion sensors, in a novel way, to detect these hidden voice commands. Our approach is based on the premise that while the crafted audio features of the hidden voice commands may fool an authentication system in the audio domain, their unique audio-induced surface vibrations captured by the motion sensor are hard to forge. Our approach extracts and examines the unique audio signatures of the issued voice commands in the vibration domain to detect the presence of hidden voice attacks. We further show that speech/speaker recognition systems are vulnerable to adversarial attacks. In particular, we demonstrate that we could successfully launch over-the-air adversarial attacks to the state-of-the-art deep neural network (DNN) based speaker recognition system in practical scenarios. In such scenarios, the adversarial examples are played through a loudspeaker to compromise speaker recognition devices.




